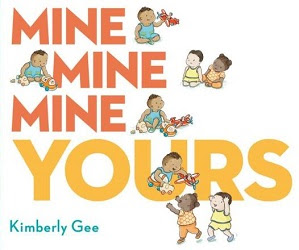
Whose? Mine, Mine, Mine, Yours by Kimberly Gee
A hopeful young dad welcomes two toddlers over for a playdate, with predictable results.
At first, the tots begin cheerily with a game of hide and seek. Things are going well as Dad searches for the three hiding together under a blanket.
There are giggles and smiles all around as the three walk UP and DOWN over the little bridge and then form a line to walk UNDER it, 1, 2, 3, with Dad playing traffic light.
STOP! STOP! STOP! GO!
There's time for a very messy snack and an individual wash up of hands and faces.They take turns "cleaning up" the kitchen, and the two moms return to claim their little ones after their very first play day with what we can hope will be long-time friends, in Kimberly Gee's Mine, Mine, Mine, Yours! (G.P. Putnam's Sons, 2021). A toddler book which reinforces social skills and the concept of opposites, (beginning with the title), author-illustrator Kimberly Gee's tots and one very busy dad make for quite a story of a first friends-over-to-play-party. Illustrator Kimberly Gee's believable little ones have a charming naivete' all their own, and the story ends with everyone happy.
Share this one with Gee's companion concept book, Up, Up, Up, Down!
Labels: Concept Books, Sharing--Fiction (Ages 1-4)


1 Comments:
It Tears me Up Whenever we receive complaints from Clients About Their Experience With the Hackers They Met Before They Heard about us.
These Days There Are alot of Hackers Online, You Just Have to Be Careful about who you meet for help, because many people now don't know who to ask for help anymore but there's actually a solution to that which I am giving you for free, Don't go out there seeking for Hackers Yourself, Because the probability of getting a Real Hacker Out there Is Very Slim . ❌❌ ❌ Most Of Them are actually not who they say they're, they are just here to Rip people Off, You Can Always Identify Them With Their False Advertisements and False Testimonies Trying To Lure you Into their Arms, And most of them use yahoomails, gmails and other cheaper email providers which could easily expose their vulnerabilities, Please Don’t Fall For Them🚷 Come To Think Of It, Why would a Legit Hacker Be using a gmail or a cheap email provider that exposes his vulnerabilities????⚠️⚠️⚠️
Well, Our Purpose Here Is To Link You Up With Top Legit Hackers With Great Online Reputations and Impressive LinkedIn Profiles That’ll Blow Your Mind.
☑️ COMPOSITE FIRMWARE SECURITY SPECIALISTS is here to Provide you with The Best Hackers, So you can get saved from The Arms of the Fake Hackers❌❌.
☑️All our Specialists are well experienced in their various niches with Great Skills, Technical Hacking Strategies And Positive Online Reputations And Recommendations🔘
They hail from a proven track record and have cracked even the toughest of barriers to intrude and capture all relevant data needed by our Clients.
We have Digital Forensic Specialists, Certified Ethical Hackers, Software Engineers, Firmware Security Experts, Private investigators and more. Our Goal is to make your digital life secure, safe and hassle free by Linking you Up With these great Professionals such as JACK CABLE, ARNE SWINNEN, SEAN MELIA, DAWID CZAGAN, BEN SADEGHIPOUR And More. These Professionals are Well Reserved Professionals who are always ready to Handle your job with great energy and swift response so that your problems can be solved very quickly.
All You Need to Do is to send us a mail and we’ll Assign any of these specialists to Handle your Job immediately.
☑️ Below Is A Full List Of Our Services:
▪️ FUNDS RECOVERY ON SCAM INVESTMENTS, BINARY OPTIONS TRADING and ALL TYPES OF SCAMS.
▪️ WEBSITE AND DATABASE HACKING 💻
▪️ CREDIT REPAIR. 💳
▪️ PHONE HACKING & CLONING (giving you 📱 Unnoticeable access to everything Happening on the Target’s Phone)
▪️ CLEARING OF CRIMINAL RECORDS ❌
▪️ SOCIAL MEDIA ACCOUNTS HACKING 📱
▪️RECOVERY OF DELETED FILES 📤
▪️LOCATION TRACKING 📌
▪️BITCOIN MINING ⛏ And lot More.
☑️ CONTACT:
.....
firmwarehacks@gmail.com
🔘2021 © composite firmware specialists
🔘Want faster service? Contact us!
🔘All Rights Reserved ®️
By FIRMWARE HACKS, at 1:52 PM
FIRMWARE HACKS, at 1:52 PM
Post a Comment
<< Home